Distributed denial of provider (DDoS) assaults are increasingly more true of existence for any business with a web presence. For any enterprise, large or small, it’s no longer a matter of “if” you may get hit with a DDoS attack, however “while.” And without a 3rd celebration issue like Incapsula, WordPress websites are increasingly more liable to bots handing over DDoS assaults.
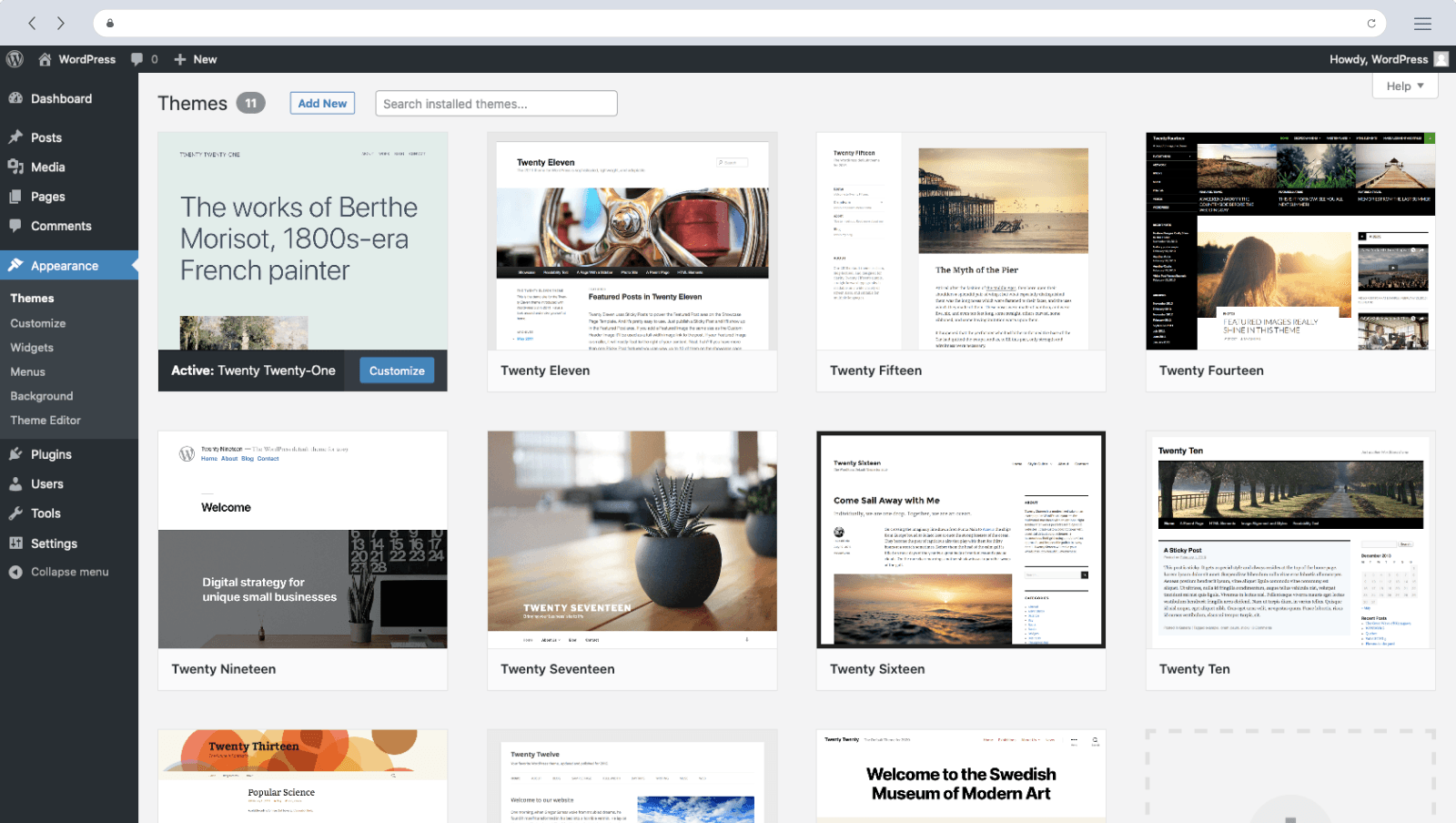
WordPress Site
The more famous a platform is, the more likely it’ll become a goal for attacks. And WordPress is by far the most popular platform on the Internet. The CMS money owed for almost 60 percent of the marketplace percentage and incorporated a brilliant 25 rate of all websites throughout the web. Of all the millions of sites, 60 percent are running older models of WordPress or more recent but unpatched variations, which are at risk of becoming bots to participate in an assault.
Based on industry reviews and present-day trends, the prevalence of DDoS assaults is growing rapidly, and getting better from the damage of an assault can also take months or years. Over half of the respondents in an Incapsula survey (52%) stated their employer needed to replace software/hardware or that it had lost sales. An additional 43 percent confirmed that their organization lost consumer trust.
Patching WordPress Won’t Stop a DDoS Attack.
“The biggest safety vulnerability is a previous WordPress component,” says Eric Murphy, Director of Security at WP Engine. “The most crucial component human beings must be doing is making sure their WordPress core, subject matters, and plugins are all saved up-to-date. Understanding the OWASP Top 10 further enables customers, developers, and engineers to defend their WordPress belongings.”
Murphy’s right. Patching your WordPress website online will preserve your site’s stability and prevent many assaults. But it can prevent a determined DDoS attack. Even if you hire the maximum diligent WordPress admin to stare at a screen, who checks and applies patches as quickly as they’re released, and tirelessly keeps the website up to date, your website online can still be introduced to its knees with the aid of a DDoS attack costing your business income, resources and recognition.
Another reason your website is vulnerable to DDoS assaults is that they’re sourced from a growing matrix of unpatched IoT gadgets that span the Internet. Many (maximum?) providers bringing devices online aren’t prioritizing protection but choose customers’ ease of use. The reasoning is that each time a further layer of safety is required, it may affect income.
Yet some other motive that safety is an afterthought for IoT devices — even in the age of the DDoS hack — is that vendors are bringing their merchandise to market as fast as feasible. If they get it to call first, they can win or even dominate the market percentage. So, the product is dropped with an immature or non-existent security framework with a plan to repair the security issues later. But in the period in between, your WordPress website is hit again via some other assault vector.
The proliferation of IoT devices is immediately growing the range and energy of DDoS attacks. Nearly any smart tool may be leveraged in a DDoS assault. A couple of white hat hackers demonstrated how a Nest thermostat would be used to extort cash from its customers. Google owns the nest and can manage to pay to patch the vulnerabilities, but many smaller companies with IoT gadgets do not have enough money to fix them too often.
Yoast SEO
The IoT denial of the carrier can take nearly any form. In February of 2017, the school and college students at an American university were denied Internet access because its vending machines and mild bulbs had been pinging seafood-associated internet websites.
Wait, what? Light bulbs? Yes, even mild bulbs can now be used in DDoS attacks. Those cool Philips Hue lighting fixtures were these days made to flash S-O-S in Morse code in a building after being infected by using a virus introduced by a drone soaring out of doors. See it here. And researchers say that’s only the start. Soon, the vulnerability on your light’s running device can be utilized in a huge DDoS attack.
Then, there are the IoT devices that don’t have vendors. Built on freeware, Raspberry Pi computers can do nearly anything. A maker’s dream, these less expensive computer systems can be constructed to flow films, take a look at the contents of your fridge, order stuff from Amazon — absolutely whatever you could think about. But that flexibility additionally comes at a fee. Today’s generation of Raspberry Pi computers are wirelessly connected to the Internet, so there could be plenty more in the wild.
IoT Cisco
These reasonably-priced computers had been created to educate computing. Like the carriers freeing a brand new product, protection isn’t the pinnacle when a student is constructing a birdhouse webcam or Kobi device, making the proliferation of these little PCs the following front for cyber warriors.
Add to that the vulnerability of top old unpatched Windows PCs, like XP, and you have been given a tech cocktail to be constructed for attacks. Over the ultimate year, an Imperva 2013-2014 DDoS Threat Landscape report factors to a 240 percent increase in a botnet (i.e., a Network of zombie computer systems utilized by offenders to launch DDoS assaults) assault interest. In Q4 2013, the variety of such assaults rose by 42 percent, consistent with Verizon’s 2014 Data Breach Investigations Report.
Incapsula Protects Your WordPress Sites
Cleaning up after a DDoS is not anything brief or painful. The complete commercial enterprise is laid low with the DDoS attack. It moves from an IT/ InfoSec trouble to a corporation-extensive problem. Execs, income, advertising and marketing, and assistance all ought to re-script and manage the damage an attack will deliver.
Search Sites
Knowing that a patched WordPress website dwelling on a fixed hardware and software platform will do little to mitigate a DDoS attack, the subsequent step is to look at what can mitigate an attack. It’s an exclusive approach. The visitors desire to be inspected earlier than it reaches your website. How? Incapsula acts as an opposite proxy, so all incoming connections on your website first pass through an Incapsula server where the traffic is inspected.
If the assault ramps up, Incapsula will dedicate more resources to ensure legitimate visitors get to your website. This is hard to do on your personal. Incapsula may also make certain you maintain to look at the actual originating IP of your website visitors so there is no misplaced value.
Incapsula gives your website the safety and performance that became formerly most effective available to high-stop CMS websites. Through easy DNS settings change and the Incapsula plugin, internet site visitors are seamlessly routed through the Incapsula international network of high-powered servers. Incoming traffic is intelligently profiled in actual time, blocking even the modern web threats from state-of-the-art SQL injection assaults to malicious bots and intruding comment spammers.
Meanwhile, outgoing site visitors are elevated and optimized for quicker load instances, retaining welcome traffic speeding through. Another benefit of filtering the incoming site visitors through Incapsula is that it applies what it has discovered from other attacks in actual time. If it sees a cross-scripting attack vulnerability towards one of its customers, it may, without delay, follow that option to all its customers.

